Picture this: It’s a Tuesday morning at a mid-sized automotive parts factory in Stuttgart, Germany. The plant manager, Markus, is staring at a dashboard that’s supposed to show him real-time data from 47 different machines — but half the sensors aren’t talking to his SCADA system, and the other half are throwing error codes that nobody on the floor can decode. Sound familiar? This scenario plays out across thousands of factories every single week, and it’s exactly why IIoT (Industrial Internet of Things) integration with industrial control systems remains one of the most talked-about — and most misunderstood — challenges in manufacturing today.
In 2026, IIoT isn’t a futuristic concept anymore. It’s the connective tissue that holds modern smart factories together. But connecting IIoT devices to legacy and modern industrial control systems (ICS) — think PLCs, SCADA, DCS, and HMI systems — is far more nuanced than plugging in a cable. Let’s think through this together, step by step.
What Does IIoT-ICS Integration Actually Mean?
Before we dive into the how, let’s get crystal clear on the what. Industrial Control Systems (ICS) are the backbone of physical operations — they include:
- PLCs (Programmable Logic Controllers): The workhorses of factory floors, managing discrete machine operations.
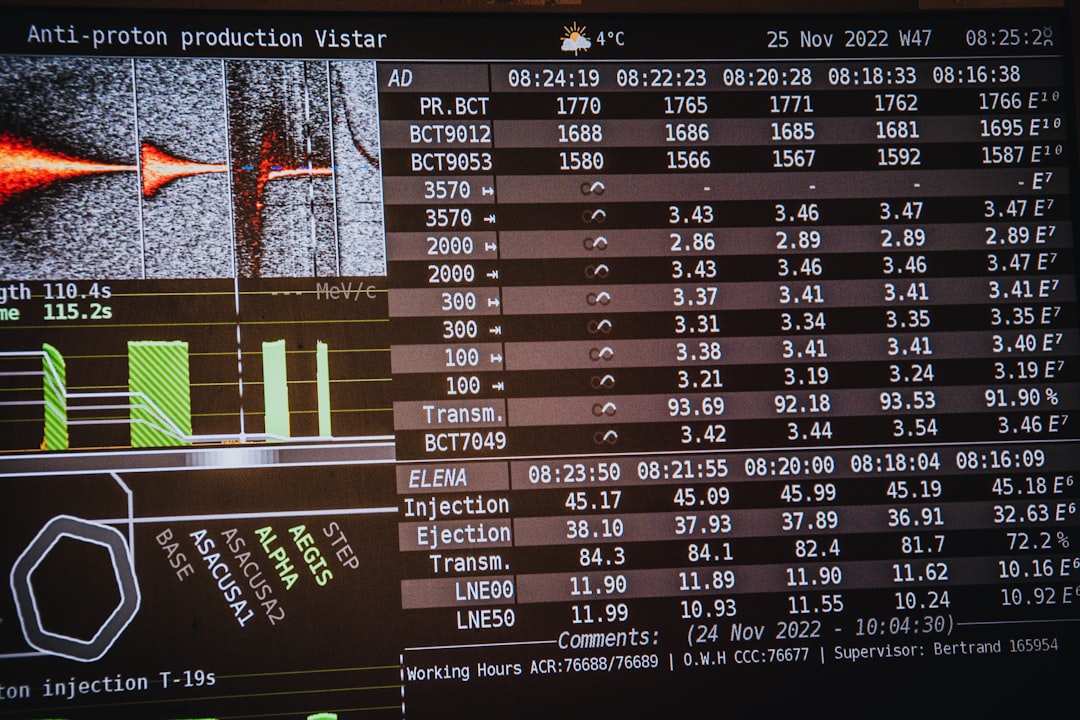
- SCADA (Supervisory Control and Data Acquisition): High-level monitoring and control across geographically distributed assets.
- DCS (Distributed Control Systems): Common in process industries like oil refining or chemical plants, handling complex continuous processes.
- HMI (Human-Machine Interfaces): The operator screens and panels that translate machine language into human-readable data.
IIoT integration means enabling these systems to share data bidirectionally with cloud platforms, edge computing nodes, analytics engines, and enterprise software (like ERP or MES systems) — all while maintaining real-time responsiveness and operational safety.
The Key Integration Protocols You Need to Know
Here’s where most people get lost, so let’s break it down practically. The “language barrier” between legacy ICS and modern IIoT platforms is a real engineering challenge. In 2026, the dominant protocols bridging this gap include:
- OPC UA (OPC Unified Architecture): The gold standard for secure, platform-independent data exchange. OPC UA supports both publish-subscribe and client-server models, making it incredibly flexible. According to the OPC Foundation’s 2026 industry report, OPC UA adoption has grown by over 340% since 2020, now embedded in over 60% of new industrial deployments globally.
- MQTT (Message Queuing Telemetry Transport): Lightweight and ideal for bandwidth-constrained environments. MQTT over 5G networks is increasingly popular for remote asset monitoring — think wind turbines, offshore platforms, or distributed pipeline sensors.
- Modbus TCP/IP: It’s old (invented in 1979!), but don’t dismiss it. Millions of legacy PLCs speak Modbus, and modern IIoT gateways almost universally support it as a translation layer.
- PROFINET and EtherNet/IP: Popular in European and North American manufacturing respectively, these industrial Ethernet protocols are now increasingly wrapped with IIoT gateway adapters.
- TSN (Time-Sensitive Networking): The emerging IEEE 802.1 standard that’s enabling deterministic, low-latency communication — critical for real-time control loops that can’t tolerate network jitter.
A Step-by-Step Integration Architecture
Let’s reason through a realistic integration approach rather than an idealized textbook diagram. Think of it as a three-layer sandwich:
Layer 1 — The Edge Layer: This is where IIoT gateways or edge computing devices (like Siemens SIMATIC IPC, Advantech UNO series, or AWS Panorama nodes) sit physically close to the machines. They collect raw data from PLCs and sensors via legacy protocols (Modbus, PROFINET, etc.), perform local preprocessing and filtering, and translate data into IIoT-friendly formats like OPC UA or MQTT JSON payloads. Critically, this layer also provides a security buffer — industrial DMZ architecture keeps OT (Operational Technology) networks isolated from direct internet exposure.
Layer 2 — The Connectivity Layer: Secure, reliable data transport from edge to cloud or on-premise servers. In 2026, this increasingly means private 5G networks within large facilities, MPLS-secured WAN links for multi-site operations, or hybrid approaches combining local edge servers with selective cloud bursting. Zero Trust Network Access (ZTNA) principles are now considered mandatory in ICS environments following the high-profile ransomware incidents of 2022–2024 that targeted OT infrastructure.
Layer 3 — The Application Layer: This is where value is actually created. Industrial IoT platforms like PTC ThingWorx, Siemens MindSphere (now Siemens Xcelerator), Microsoft Azure IoT Hub, or AWS IoT SiteWise ingest, contextualize, and visualize the data. Integration with MES (Manufacturing Execution Systems) and ERP platforms closes the loop between physical operations and business intelligence.
Real-World Examples: Who’s Doing This Well in 2026?
Theory is useful, but examples are where the rubber meets the road.
Hyundai Motor Group (South Korea): Hyundai’s Ulsan plant — the world’s largest single-site automobile manufacturing facility — completed a full IIoT-ICS integration overhaul in late 2025. They deployed a private 5G network combined with OPC UA-based edge gateways across 3,200 robotic welding stations. The result? A 23% reduction in unplanned downtime and predictive maintenance alerts now triggering an average of 6.8 days before actual component failure. Their key insight: they didn’t replace legacy PLCs (Siemens S7-300 series, many over 15 years old) — they wrapped them with modern gateway adapters instead.
BASF (Germany): The chemical giant’s Ludwigshafen complex runs one of the most complex DCS environments in the world. Their IIoT integration project — built around ISA-95 compliant data models and OPC UA information models — created a unified data fabric connecting over 200 distinct process units. What’s notable is their deliberate use of data diodes (hardware-enforced one-way data flows) for their most safety-critical reactor control loops, proving that IIoT connectivity doesn’t have to mean connectivity everywhere.
Doosan Enerbility (South Korea): Formerly Doosan Heavy Industries, they’ve been deploying AI-enhanced IIoT monitoring for their gas turbine fleet across Southeast Asia. Using Azure IoT SiteWise with custom OPC UA connectors, they now monitor over 80 operational parameters per turbine in near-real-time from a central operations center in Changwon. Fleet-wide analytics have improved turbine availability rates by approximately 4.2 percentage points — significant given that each turbine represents hundreds of millions in assets.
Common Pitfalls (and How to Avoid Them)
- Ignoring OT security from day one: ICS environments have very different security postures than IT systems. Patching cycles are slow, uptime requirements are extreme (99.99%+), and legacy systems may have zero native security features. Always design security architecture before, not after, integration.
- Data overload without context: It’s tempting to stream everything to the cloud. Don’t. Edge preprocessing — filtering, aggregating, and contextualizing data before transmission — dramatically reduces bandwidth costs and improves analytics quality. MQTT’s QoS (Quality of Service) levels and OPC UA’s subscription filtering mechanisms exist precisely for this reason.
- Underestimating change management: The human side of integration is consistently underestimated. Floor operators and maintenance technicians need to trust and understand new systems. Building intuitive HMI dashboards and investing in training is just as important as the technical architecture.
- Protocol mismatch at brownfield sites: Many older facilities have mixed vendor environments — Allen-Bradley PLCs alongside Mitsubishi drives alongside Yokogawa transmitters. A universal IIoT gateway (like Kepware’s KEPServerEX or Moxa’s ThingsPro) that supports dozens of protocols simultaneously is often the most pragmatic starting point.
A Realistic Roadmap for Getting Started
If you’re not a Hyundai or BASF with massive integration budgets, here’s a pragmatic path forward:
- Phase 1 — Assess and Prioritize (1–3 months): Audit your existing ICS landscape. Identify which machines or process areas generate the highest value if monitored. Don’t try to boil the ocean — start with two or three high-impact assets.
- Phase 2 — Pilot with Edge Gateways (2–4 months): Deploy a low-risk IIoT pilot using commercially available edge gateways. Validate protocol compatibility, data quality, and network stability before scaling.
- Phase 3 — Establish the Data Platform (3–6 months): Choose your IIoT platform (cloud, on-premise, or hybrid) and define your data models. ISA-95 and ISA-88 standards provide excellent frameworks for structuring manufacturing data hierarchically.
- Phase 4 — Scale and Iterate (Ongoing): Expand coverage incrementally. Use data from early deployments to build the business case for broader investment. Continuously review cybersecurity posture as the connected footprint grows.
The companies seeing the best ROI from IIoT-ICS integration in 2026 aren’t necessarily the ones with the biggest budgets — they’re the ones with the clearest use cases, disciplined phased rollouts, and strong collaboration between IT and OT teams.
The gap between what IIoT promises and what factories actually experience is almost always an integration problem, not a technology problem. The tools, protocols, and platforms available today are genuinely excellent. The challenge is thoughtful, patient architecture — respecting both the reliability demands of industrial operations and the analytical ambitions of the digital enterprise.
Editor’s Comment : If there’s one thing worth internalizing from everything above, it’s this: IIoT-ICS integration is a journey of progressive trust-building — between systems, between protocols, and between the people who run factories and the people who build digital platforms. Don’t rush the architecture to chase a demo. The factories that have gotten this right in 2026 started slow, thought hard about security and data governance, and scaled only after proving real value at small scale. Your legacy PLCs aren’t your enemy — they’re the foundation you’re building on. Respect them, wrap them thoughtfully, and the data you unlock will be genuinely transformative.
📚 관련된 다른 글도 읽어 보세요
- Node.js vs Bun vs Deno in 2026: Which JavaScript Runtime Actually Wins on Performance?
- 지멘스 PLC vs 미쓰비시 PLC 비교 리뷰 2026 — 현장 엔지니어가 실제로 느끼는 차이
- 풀스택 개발자 취업 현실 2026: 화려한 타이틀 뒤에 숨겨진 진짜 이야기
태그: [‘IIoT integration’, ‘industrial control systems’, ‘OPC UA MQTT’, ‘SCADA IIoT’, ‘smart factory 2026’, ‘ICS cybersecurity’, ‘edge computing manufacturing’]
Leave a Reply